- Published on
ZorroSign Attends Arizona Cybersecurity Summit 2022
- Authors
-
-
- Name
- Michael Jones
-

ZorroSign team members, Cassidy Alexander, Kristen Harder, and Michael Jones were pleased to attend the ninth annual Cybersecurity Summit in Scottsdale on May 12, 2022, hosted by the Arizona Technology Council, Arizona Commerce Authority, and Arizona Cyber Threat Response Alliance (ACTRA).
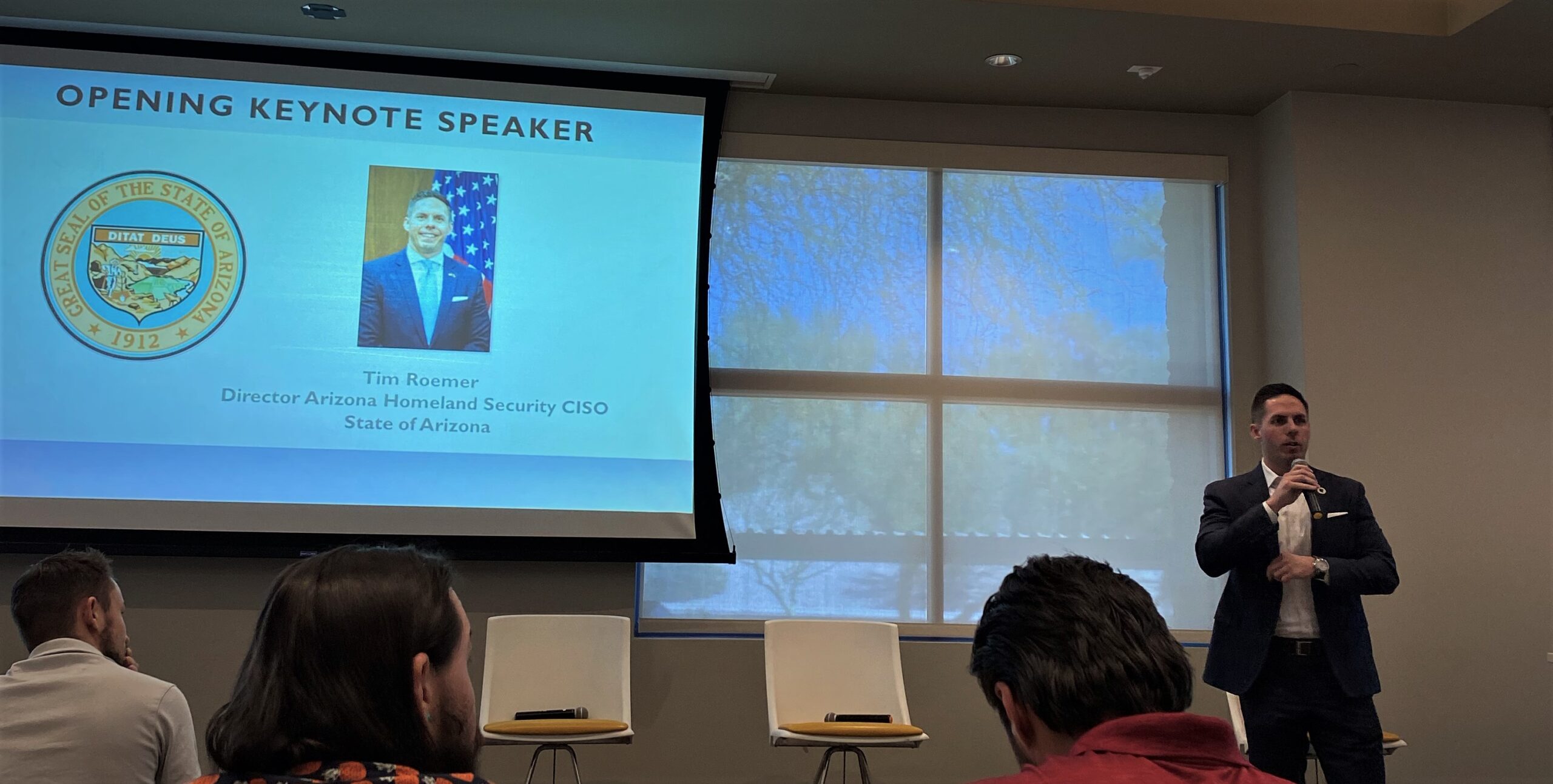
The educational event provided an opportunity for government and business leaders to learn about the threats, vulnerabilities and consequences related to data security and privacy matters via panel discussions, keynote speakers—Tim Roemer, Director Arizona Homeland Security/CISO State of Arizona, and John Davis (Major General, US Army, Retired), VP Public Sector at Palo Alto Networks—sponsors and other cybersecurity presentations.
Key Themes of the Summit
- The merger of cyber and physical worlds, requiring consolidated security approaches
- Zero-trust 2.0 for IT/OT security
- Sharing of security information, threats, and vigilance across the public and private sector
- Improving offensive cybersecurity capabilities to better understand new threat vectors
- Security automation and the need to elevate security against greater and greater threats with fewer and fewer cybersecurity resources
- The impact of the Cyber Incident Reporting for Critical Infrastructure Act of 2022, as signed into law by President Biden in March 2022
- Protecting supply chains
- Building cybersecurity plans not just focused on prevention but also focused on quickly recovering from successful attacks

Blockchain Architecture For Elevated Security
ZorroSign is the only company that offers a multi-blockchain platform to secure, track, and manage your digital signatures, transactions, and documentation.
By using distributed ledger technologies—originally built on Hyperledger Fabric and recently expanded to include the Provenance Blockchain—ZorroSign provides superior privacy and security, while preventing fraud and ensuring regulatory compliance.

How does this blockchain architecture contribute to cybersecurity?
Blockchains provide structural layers of protection from cybercrime—like ransomware, malware, or phishing attacks—first, by decentralizing the data set itself (preventing any one breach to access the entire data set), and second, by giving endpoints (or nodes) a quick path to recovery, even if they are themselves breached or their access ransomed.
Unlike centralized databases—which can be breached at unsecure endpoints (users and devices) or even at managed service providers (MSPs) hosting them—giving attackers complete control once they gain central access, blockchain technology distributes data physically across separate nodes. By decentralizing data storage, blockchain effectively prevents any one endpoint (even if compromised) from gaining control of the full data set.
This distributed nature defeats any attack seeking to breach a system and holistically encrypts the data files stored inside: A single endpoint node might be breached, and its files held for ransom, but the larger data set cannot be controlled by any one endpoint (or central authority) and so attackers cannot capture the full data set for encryption, ransom, and shutting down the network.
ZorroSign is a strong addition to any organization’s security stack, and brings the cybersecurity capabilities of blockchain to digital signatures and transactional documentation.
Z-Forensics Token
ZorroSign has further elevated our security through our patented fraud detection technology we call the Z-Forensics token. This unique digital solution that can:
- Prove that the individual who is performing the action to sign the document is who they claim to be (verification)
- Apply a digital equivalent of a wet-ink signature to the document (legal intent)
- Prove the authenticity of the printed or digital version of an electronically signed document, its content, attachments, and the signatures on it (authenticity)

Unlike any other digital signature solution, ZorroSign seals all our clients’ documents with the Z-Forensics token—capturing the complete audit trail and accompanying attachments and signature workflow. The token is encrypted and contains all the details about the transaction: Time stamps, user authentication, documents and attachments.
To learn more about how ZorroSign helps companies and IT departments elevate data privacy and security, please contact us or start a Free Trial today!